Zero Trust Security: Key Concepts and 7 Critical Best Practices

What is Zero Trust?
Zero trust is a security model to help secure IT systems and environments. The core principle of this model is to never trust and always verify. It means never trusting devices by default, even those connected to a managed network or previously verified devices.
Modern enterprise environments include networks consisting of numerous interconnected segments, services, and infrastructure, with connections to and from remote cloud environments, mobile devices, and Internet of Things (IoT) devices.
There is no clear perimeter in this highly diverse and distributed environment. As a result, the traditional approach, which trusts devices within the perimeter or devices connected via a virtual private network (VPN), does not provide adequate security.
The zero trust security approach helps increase security coverage for modern enterprise environments. It typically involves implementing mechanisms such as mutual authentication to check each device’s identity and integrity regardless of location. Another key practice is providing access to applications and services according to the confidence level in device identity and health.
In this article:
Why is Zero Trust Security Important?
A zero trust model helps protect against many attacks, including data and identity theft. It helps protect company data, decrease breach risk and detection time, improve visibility into network traffic, increase control across cloud environments, and conduct compliance auditing.
There is no clear perimeter
Traditional security strategies, like firewalls and VPNs, create a perimeter around a network that allows authenticated devices and users to traverse the network and access resources. This approach is ineffective for securing modern environments that allow many users to work remotely and run sensitive assets in the cloud.
Ransomware is on the rise
Zero trust can help create a robust security defense against ransomware attacks. Excessive permissions, human error, and lack of security maintenance are the root cause of many cyber attacks, including ransomware. Zero trust security can prevent ransomware, or at least limit its effect, by segmenting the network, deploying secure user identity and access management.
The attack surface keeps expanding
Zero trust helps minimize the scope of the attack surface by providing internal and external users with limited access to resources, keeping all other resources completely hidden. It also helps securely implement the threat monitoring and detection capabilities needed to prevent ransomware attacks and data exfiltration.
How To Build a Zero Trust Architecture
Zero trust is not a specific solution – it is a security paradigm that can be implemented using different technologies and approaches. Here are some of the technology components commonly used to build a zero trust architecture.
Zero Trust Network Access (ZTNA)
ZTNA is a core component of zero trust at many organizations. It is a solution for secure remote access that implements zero trust security principles and application-specific permissions.
When remote workers request access to company assets, the ZTNA solution grants them access to certain resources on a case-by-case basis. When granting access, the solution considers role-based access controls as well contextual authentication data, like location, time restrictions, and user group or role.
You can deploy ZTNA as part of a secure access service edge (SASE) solution that combines network security with network optimization capabilities like software-defined WAN (SD-WAN). Deploying SASE enables organizations to transition from perimeter-based security to a zero trust architecture designed for the distributed enterprise.
Microsegmentation
A zero trust architecture relies on network segmentation and the security controls between network segments. The goal is to protect sensitive data and services against unauthorized access and prevent threats from spreading.
Microsegmentation involves dividing a network into secure and logical units by applying policies that control access to data and applications. Here are the main differences between traditional network segmentation and microsegmentation:
- Network segmentation applies hardware controls mainly to client-server traffic flowing between data centers (north-south data flows).
- Microsegmentation employs software and applies to server-to-server traffic flowing between applications (east-west data flows).
By breaking a network into smaller pieces, microsegmentation limits the traffic that can laterally traverse the network. As a result, it increases the overall security of the network and its assets. You can apply microsegmentation to cloud environments and local data centers.
Next-Generation Firewall
A next-generation firewall (NGFW) is a third-generation technology you can implement in software or hardware. It enforces security policies at the port, protocol, and application levels to detect and block sophisticated attacks. In a zero trust architecture, NGFW is commonly used to implement network and application segmentation policies.
NGFWs use various capabilities of traditional firewalls, such as packet filtering, port address translation (PAT), network address translation (NAT), virtual private networks (VPNs), and URL blocking.
NGFWs combine traditional capabilities with quality of service (QoS) functionality and advanced features like intrusion prevention, deep-packet inspection, reputation-based malware detection, application awareness, and SSL and SSH inspection. Application-specific capabilities help block the growing amount of application attacks occurring at layers 4-7 of the OSI network stack.
Data Loss Prevention
Data loss prevention (DLP) helps prevent unauthorized access to sensitive information. It ensures unauthorized parties cannot send critical or sensitive information outside the network. In a zero trust environment, DLP is important to detect and block unauthorized data flows.
DLP solutions can monitor, detect, and block sensitive data from being transferred outside the organization. It typically involves monitoring entry to the networks as well as any data attempting to leave the network.
7 Best Practices for Zero Trust Security
1. Verify all Devices
It is critical to verify not only users but also devices. Zero trust security extends verification to endpoint devices. You can implement device verification in various ways, for example, ensuring all devices accessing internal resources meet predefined security requirements. Ideally, you should look for a solution that enables you to use easy user onboarding and offboarding for tracking and enforcing the status of all devices.
2. Implement the Principle of Least Privilege
In a zero trust environment, it is the principle of least privilege (PoLP) that determines what users and devices can access. The goal is to ensure each user is assigned only the privileges necessary to complete their tasks. For example, a software developer does not need access to financial records.
You can expand least privilege access to also include just-in-time privileged access, which restricts privileges to the specific times when a user needs these privileges. It often involves creating one-time-use credentials and expiring privileges.
3. Implement Zero Trust Policies
A strong zero trust security implementation requires policies. Creating and implementing these policies is a critical phase but also time-consuming. It requires an accurate understanding of the protection surface to ensure the appropriate traffic flow is denied or allowed. Ideally, you should create granular policies and enforce them on all network workloads using security tools.
When creating zero trust policies, you need to determine key factors, including the users, the access and privileges they need to perform their job, and the time they require this access. You should also assess where users and endpoints are located, why they need access to the requested data, and determine how the organization approves or allows this access.
4. Monitor and Audit
Monitoring and auditing are key components in a zero trust security implementation. You can identify suspicious activity in real-time by monitoring and reviewing user activity across the corporate network. Achieving this visibility is critical for users with administrative rights because they have more access permissions and access to highly sensitive data.
5. Combine Zero Trust with On-Call Management
Zero trust systems generate alerts about suspicious network traffic and login activity. Unlike alerts from traditional tools, which included a large number of false positives, these are high quality alerts, based on behavioral analysis, which must be immediately handled by security or operations teams.
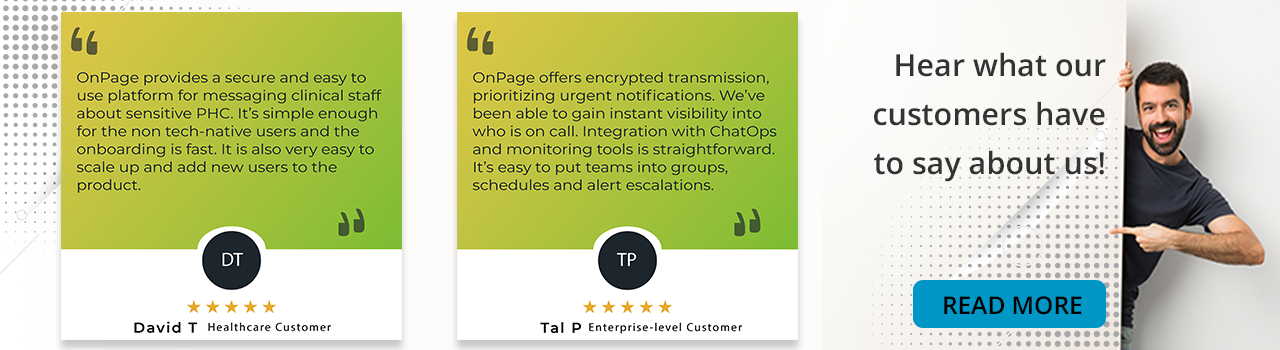
It is highly beneficial to use an on-call management system like OnPage to escalate zero trust alerts to the relevant team members. This makes it possible to respond to threats and calibrate zero trust systems in real time to adapt to current traffic patterns.
Try OnPage for FREE! Request an enterprise free trial.
6. Adopt Attribute-Based Controls
Adopt attribute-based controls for authorizing access to resources across the security stack, including cloud and on-premises applications, APIs, infrastructure, and data. These controls enable administrators to adjust and enforce access policies easily and block suspicious events in real-time.
7. Consider Your End Users
To be effective, a zero trust security strategy must consider end-users. If users do not or cannot use the strategy, it will not provide the intended security coverage. To make it easier for end-users, the strategy and tools you implement should be as frictionless as possible, offering a SaaS-like experience.
Conclusion
In this article, we explained the basics of zero trust security and provided 7 best practices that can help you implement zero trust more effectively:
- Verify all devices, whether inside or outside the organization
- Implement least privilege using zero trust technologies
- Implement zero trust policies and enforce them for all traffic
- Monitor and audit to achieve visibility over network activity
- Combine zero trust with on-call management to ensure rapid response to anomalies
- Adopt attribute-based controls to allow more granular access management
- Consider end users and ensure zero trust does not interfere with productivity
We hope this will be useful as you take your first steps towards zero trust security in your organization.