What IT Pros Can Learn from the Marriott Data Breach

Despite the best efforts of individuals to protect their own data, they cannot always account for the cybersecurity shortcomings of larger organizations such as their employers, financial institutions, and healthcare providers entrusted with their personal information.
Recently, it was made painfully apparent that hotels should also be added to this list of vulnerable entities based on the most recent Marriott data breach.
What Happened in Marriott’s Data Breach?
As first reported on DataBreaches.net and then widely shared across business and tech media, 20 gigabytes of Marriott International’s data were compromised as a result of cybercriminals’ successful social engineering targeting an employee at the BWI Airport Marriott in Maryland.
The employee is reported to have granted remote access to their computer after falsely believing the malicious outreach was legitimate, allowing cybercriminals to take control and steal data from the world’s largest hotel chain.
While Marriott stated that most of the 20 gigabytes compromised in this attack was “non-sensitive internal business files regarding the operation of the property,” personal data and credit card information of hotel guests were revealed to have been compromised in the breach.
Marriott’s cybersecurity is facing special scrutiny given their alarming track record of breaches in recent years, but this is a great opportunity for any organization entrusted with protecting valuable data to ask themselves if they could stop a similar attack.
Based on the most recent Marriott data breach, IT pros must prioritize:
- Recognizing Social Engineering
- Continuing Cybersecurity Education
- Improving Incident Response Communications
Recognizing Social Engineering
We’d all like to believe that we can easily recognize phishing emails or otherwise too-good-to-be-true solicitations. The most cunning cybercriminals know this, however, and are using increasingly inconspicuous social engineering tactics to trick their targets.
Social engineering is a phrase encapsulating a range of different techniques designed to manipulate targets through human interaction. Cyber criminals will vigorously research the organizational structure of target companies, as well as the personal information of the employees they seek to contact.
The result is personalized, realistic solicitations that can fool even employees who believe they are able to weed out phishing attempts.
An example of social engineering is when cyber criminals target lower-level employees in large organizations by impersonating top executives in the company; after all, who could say no to the CEO reaching out to them specifically with an urgent emergency?
Continuing Cybersecurity Education
The digital transformation of the working world has been filled with welcome innovations, but has also brought about new challenges for IT leaders. Especially after remote work exploded during the pandemic, more employees are logging into work from around the world: from their home, while traveling, or even from public WiFi networks.
Additionally, the increasing number of professionals requiring access to digital resources to do their jobs at all levels of organizations creates a plethora of potential targets for cybercriminals beyond just leadership and IT professionals.
As was the case in the Marriott data breach, any employee with access to an organization’s digital resources could be the target of an attack. Security leaders must educate their employees at all levels about how to diligently ward off evolving cybersecurity threats. It is imperative to create a dedicated channel for colleagues to proactively report suspicious communications or potential threats.
Improving Incident Response Communications
Even with the best prevention and monitoring systems in place, the ability to resolve issues promptly and communicate effectively when they unfold is crucial to any organization’s incident response plan. In the event of cyberattacks or breaches, every second counts and miscommunication can lead to inefficient or even counterproductive incident resolution efforts.
While the full details of Marriott’s incident response are not known, it was reported that they were able to resolve the breach within 6 hours and that hundreds of affected stakeholders were subsequently informed of their data’s compromised status.
Would your IT team be able to respond to a breach that quickly, and if not what would be the financial and reputational cost of the damage that could be done in six hours or less?
IT teams looking to drive faster resolution to threats must adopt an incident alert management platform to improve security alert visibility. These systems sit at the center of security ecosystems, managing the distribution of high-priority alerts to the right on-call cybersecurity analyst — wherever they are.
With this integration in place, the alerts generated automatically by your cybersecurity and monitoring tools will be delivered promptly to your on-call team members, ensuring that no incidents are left unresolved for extended periods of time.
Try OnPage for FREE! Request an enterprise free trial.
Elevate Your Incident Response with OnPage
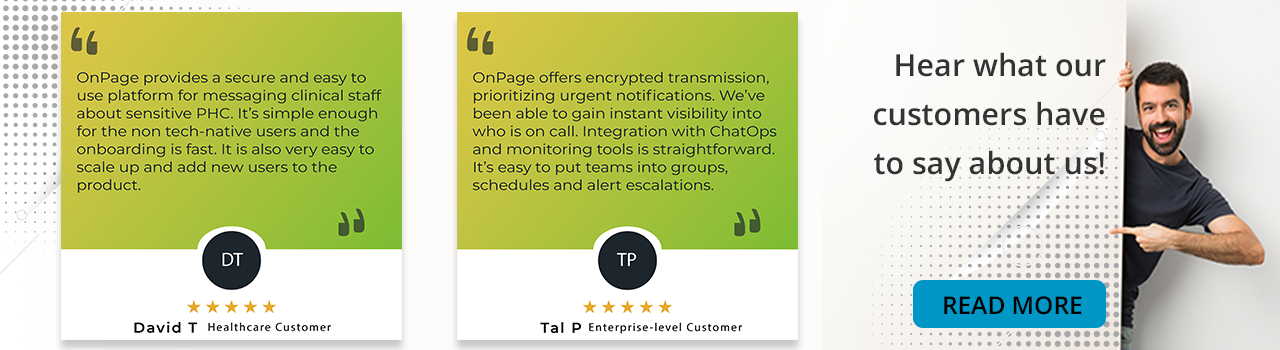
With no such thing as a “cybersecurity-immune” organization anymore and each passing year marking a new record for security failures, businesses must give equal weightage to tools that allow them to prevent and respond effectively to security incidents. To that end, organizations must reinforce their incident response capabilities with OnPage’s alert management tool.
OnPage’s incident alert management system has strengthened the incident response capabilities of thousands of organizations with ALERT-UNTIL-READ messages, on-call scheduling, and detailed post-incident reporting.
Supporting a versatile range of integrations including AWS CloudWatch, ServiceNow, and ConnectWise, OnPage is a seamless addition to your incident response workflows.
To learn more and request a demo, visit OnPage.com or give us a call at +1 (781) 916-0040.