What Is a Secure SDLC?

What Is a Secure SDLC?
The Software Development Lifecycle (SDLC) framework defines the entire process required to plan, design, build, release, maintain and update software applications, including the final stages of replacing and decommissioning an application when needed.
A Secure SDLC (SSDLC) builds on this process, integrating security at all stages of the lifecycle. When migrating to DevSecOps (collaboration between Development, Security, and Operations teams), teams typically implement an SSDLC. This involves reviewing the traditional SDLC and ensuring that, alongside functional requirements, security aspects are taken into account by all teams participating in the process.
In this article:
- Importance of a Secure Software Development Life Cycle
- Embedding Security Into All Phases of the SDLC
- Best Practices to Secure the SDLC
Importance of a Secure Software Development Life Cycle
As organizations undergo digital transformation, they aim to release software regularly, deploying new versions on a daily or even hourly basis. This is a major challenge in itself, and makes it more difficult to integrate security into the process. In the past, security was a final stage at the end of the development process, but this is impractical and inefficient in a modern SDLC.
To support high development velocity, organizations need to include security at every stage of the SDLC, rather than running security tests at the end. A Secure SDLC is an effective way to incorporate security into the development process, without hurting development productivity, and contrary to the belief that security interferes with the development process.
A key aspect of the SSDLC is to bring together all stakeholders involved in the project to ensure applications are secure. Developers can start by learning secure coding techniques and tools available to improve security. It is very important to use automated tools to quickly identify security risks in code and build artifacts—this helps developers identify security fixes and address them quickly during early development stages.
Management teams can use the secure SDLC as a strategic approach to improve overall security of software projects. For example, managers can perform a gap analysis to understand the organization’s current security policies and their effectiveness.
Embedding Security Into All Phases of the SDLC
Each stage of the SDLC requires its own security implementation, tools, and DevOps automation strategies.
Requirement Planning
In this stage, new functional requirements are gathered from stakeholders. It is important to identify security considerations related to the functional requirements for a new release. For example, if the functional requirement is to allow users to log in, the security considerations will include questions like:
- Do we build authentication ourselves or use an external provider?
- What authentication protocol will be sufficiently secure?
- Will there be multi-factor authentication or single sign-on (SSO)?
Architecture and Design
The team must follow architectural and design guidelines from the previous stage, and attempt to address the potential risks. If a vulnerability is addressed early in the design phase, it eliminates the need to detect and remove it during the development phase, which has a higher cost. Processes such as threat modeling and architectural risk analysis make the development process simpler and safer.
It is especially important to evaluate third-party software components to ensure that third parties have not introduced their own vulnerabilities into the software. This can prevent devastating supply chain attacks.
Development
The development stage involves writing the code for the application. In an SSDLC, development must be done using secure coding standards. Programmers should be up-to-date on the relevant security standards and how to apply them to their current projects.
In addition, developers need to properly implement security design patterns and frameworks. There should be a clear security architecture for the software projects, which developers can follow. Development will only be considered “done” if appropriate security patterns are used.
Furthermore, automated tools should scan code on the fly and notify developers of security issues, such as including an open source library that has known vulnerabilities.
Testing and Verification
The application now goes through a full test cycle to ensure that it meets the original design and requirements. This is a good place to deploy automated security tests. If these tests do not pass, the application should not be promoted to further stages.
Typically, automated security tools will be deployed as part of a continuous integration / continuous delivery (CI/CD) pipeline that has several “gates” controlling whether a new version should be released. These gates should include:
- Unit tests to validate individual components of the application.
- Functional tests that exercise the critical paths in the application.
- Security tests that identify if important security controls are in place and whether components contain any vulnerabilities.
- Ensuring software artifacts do not contain secrets (such as access credentials to a database). These should be dynamically inserted in production.
Maintenance
Even after a release has passed all security tests, there may be new security issues discovered in production. Keep in mind that new security vulnerabilities are discovered all the time, so even secure software can become insecure over time. At this stage, teams should monitor production environments, identify bugs and security risks, and invest efforts to remediate them.
Security practices must be followed throughout the software maintenance process. In particular, products must be constantly updated to ensure all components have the latest security patches.
Best Practices to Secure the SDLC
Prepare Your Organization
Make sure your organization is fully prepared for secure software development. Start by determining the security requirements and mapping out the people, processes, and tools involved.
Use training and management support to prepare the organization for the change. Other aspects of preparation include implementing tools to automate processes, and securing environments and endpoints for development.
Protect Development Infrastructure and Assets
Organizations must protect the source code of their software, including configuration as code. How you do this depends on the situation:
- Open source projects only need to protect the integrity of their code to prevent attackers from adding malicious code.
- Proprietary software projects need to protect confidentiality to prevent theft of intellectual property.
- All organizations need to secure their CI/CD pipelines to prevent compromise and sabotage by internal or external threat actors.
Respond to Vulnerabilities
Vulnerabilities are inevitably found in software—they might be discovered by your customers, security researchers, or by attackers. Organizations are expected to respond quickly when vulnerabilities are discovered in their software. Knowing about a vulnerability and failing to respond to it can have a major impact on the reputation of a software development or even a mobile app development organization.
A Vulnerability Disclosure Plan (VDP) and related policies provide an organizational process for analyzing new vulnerabilities, quickly identifying remedial actions, implementing them, and testing software changes to verify the fix. A VDP can help your organization prepare in advance for the next critical vulnerability.
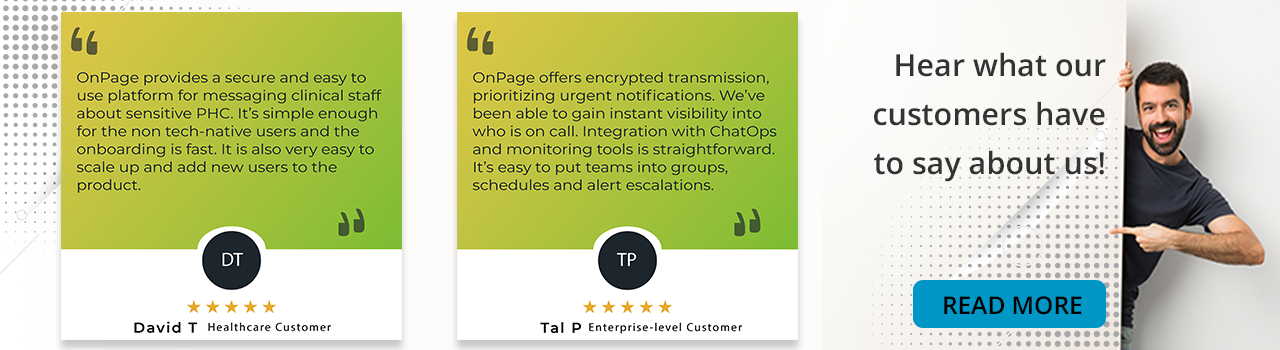
It is also important to have robust monitoring in production environments and raise alerts when suspicious activity occurs. Incident alerting tools like OnPage can help you deliver alerts to relevant personnel, ensure they respond, and automatically escalate the alert if necessary.
Try OnPage for FREE! Request an enterprise free trial.
Conclusion
In this article, we explained why it is important to create a secure SDLC, showed how to secure all phases of the development lifecycle, and provided three essential best practices for adopting an SSDLC:
- Prepare your organization—keep in mind that the transition to an SSDLC is a cultural change and must involve training and organizational alignment.
- Protect development infrastructure—ensure that the CI/CD pipeline and all related tools are locked down and secure.
- Respond to vulnerabilities—because no SSDLC is perfect, ensure you have a policy and process to respond when security vulnerabilities are discovered in production.
We hope it will be useful as you shift left and transition your organization to a secure development lifecycle.